Connect your AWS account with Site24x7 using cross-account IAM Role support.
Before we get into the nitty-gritty details of Identity and Access Management (IAM) roles, role ARNs, trust policies, and similar topics, we want to provide some context on how Site24x7 collects performance counters for various AWS infrastructure components using our CloudWatch integration.
The backstory: Key-based access
Site24x7 accesses the CloudWatch API every five minutes, automatically discovering various supported AWS services and collecting performance metrics and metadata from them. The API requests are authenticated by access keys (secret access keys and access key IDs generated during IAM user creation), and are authorized by permissions (policy templates assigned to the IAM user).
Although creating IAM users is an excellent way to enable access to your AWS account, it's not foolproof. Sharing long-term credentials has always had liabilities attached to it; a single slip-up can result in a third party gaining access to your AWS resource. Here at Site24x7, we take security seriously. The access keys that you share with us are encrypted in our database. Rest assured that we have mitigated?if not eliminated?the chance of your credentials getting compromised from our end. In spite of all this, we feel that if there's anything we can do to help you connect your AWS account in a more secure fashion, we should do it. Today I'm happy to say that this endeavor has come to fruition.
AWS customers and managed service providers (MSPs) can now use Site24x7 to securely connect their AWS account and their customers' accounts using cross-account IAM roles.
So, what's all this about IAM roles?
Cross-account IAM roles allow an IAM entity in one AWS account to access one or more resources running in another AWS environment and perform read/write actions. In Site24x7's case, you can create a cross-account role between Site24x7's AWS account and your AWS account (preferably the one where you are running your production services). The following steps will show you how to enable role-based access:
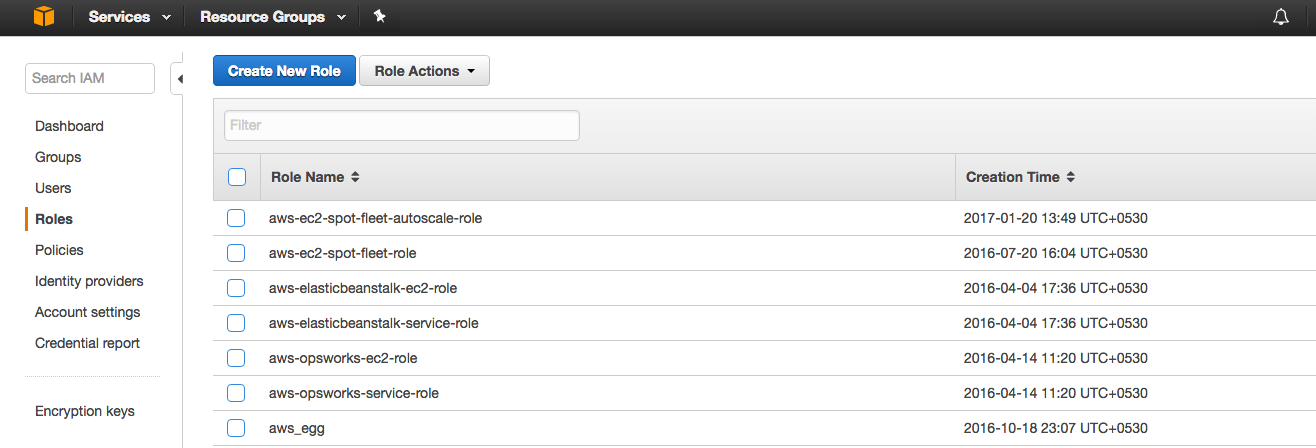
1. First, log in to your AWS account and navigate to the AWS IAM console. In the navigation pane, select Roles and get started by clicking on Create New Role.
2. Provide an appropriate role name and continue by selecting Role for Cross-Account Access. Then select the Provide access between your AWS account and a 3rd party AWS account option.
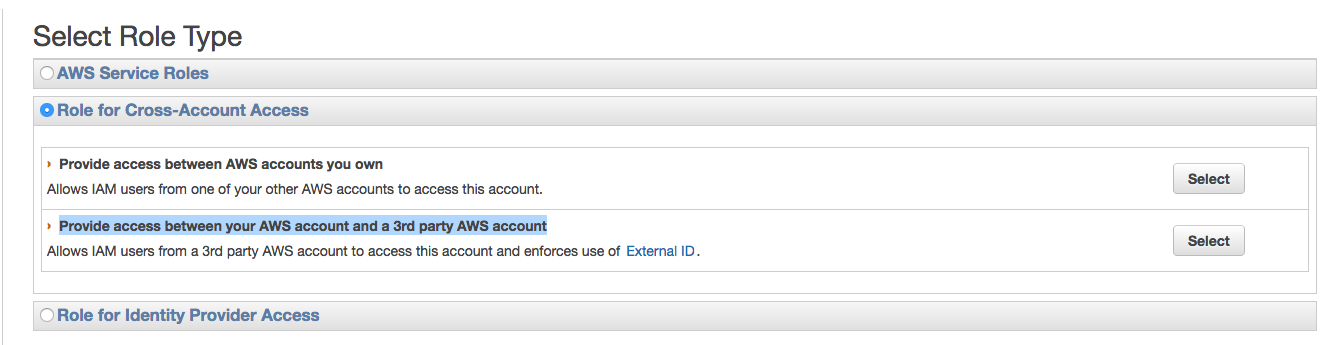
3. Next, create a trust policy for the role. Enter Site24x7's AWS account ID and your external ID (a unique ID generated in the Site24x7 console).

As discussed earlier, API requests are usually authenticated using access key IDs and secret access keys generated during IAM user creation. However, in the case of cross-account IAM roles, Site24x7 sends a request to the Assume Role API to obtain temporary security credentials. Each Assume Role API call includes both the account ID and the external ID, and the request is validated only if the parameters match the details provided above.
Site24x7 generates GUIDs for external IDs; we also make sure that no two accounts get assigned the same value. Essentially, by using cross-account IAM roles, you can lock down your AWS account from any unauthorized access.
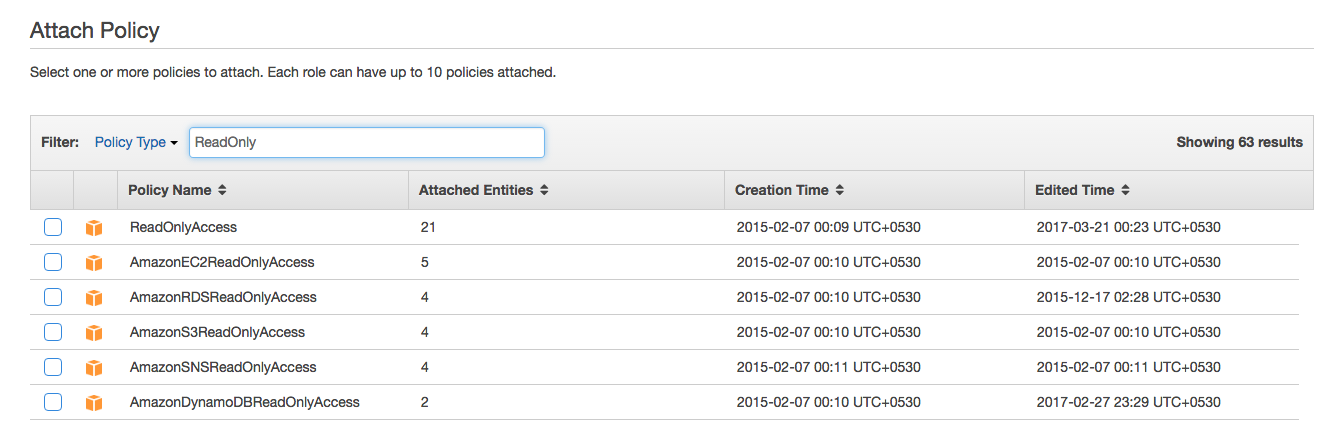
4. Once you are done establishing trust between your account and Site24x7?s AWS account, you can go ahead and define the access policy. This can either be done by assigning the default read-only policy or by pasting a custom policy JSON. The chosen policy will determine the level of access that Site24x7 gets and will be embedded into the role you create.
5. Once you create the role, log in to Site24x7. Navigate to the
AWS add monitor form and paste the role ARN.

6. After a role has been established, you can update the trust
policy, edit policy permissions, and revoke active sessions at your discretion
By bringing in support for cross-account IAM role access, we hope to alleviate any little apprehension that you might have had about connecting your AWS account with Site24x7. So, log in to your Site24x7 account now! (If you don't have one and want to get started, sign up here). Follow the instructions on this page to connect your AWS account, then make full use of our monitoring capabilities without worrying about any security issues. Happy monitoring!