Why use GuardDuty with Site24x7?
Categorized threat analysis
Centralized security account
No additional agents
Push alerts easily
Intelligent threat detection
Simple to scale
Effective enterprise AWS security
Automatically segregate the threats into different categories and obtain insights about each region, action, and types of resources affected for each threat reported as a GuardDuty finding. Thwart security breaches by unmasking not only basic misconfigurations, but also complex violations across several configured services.
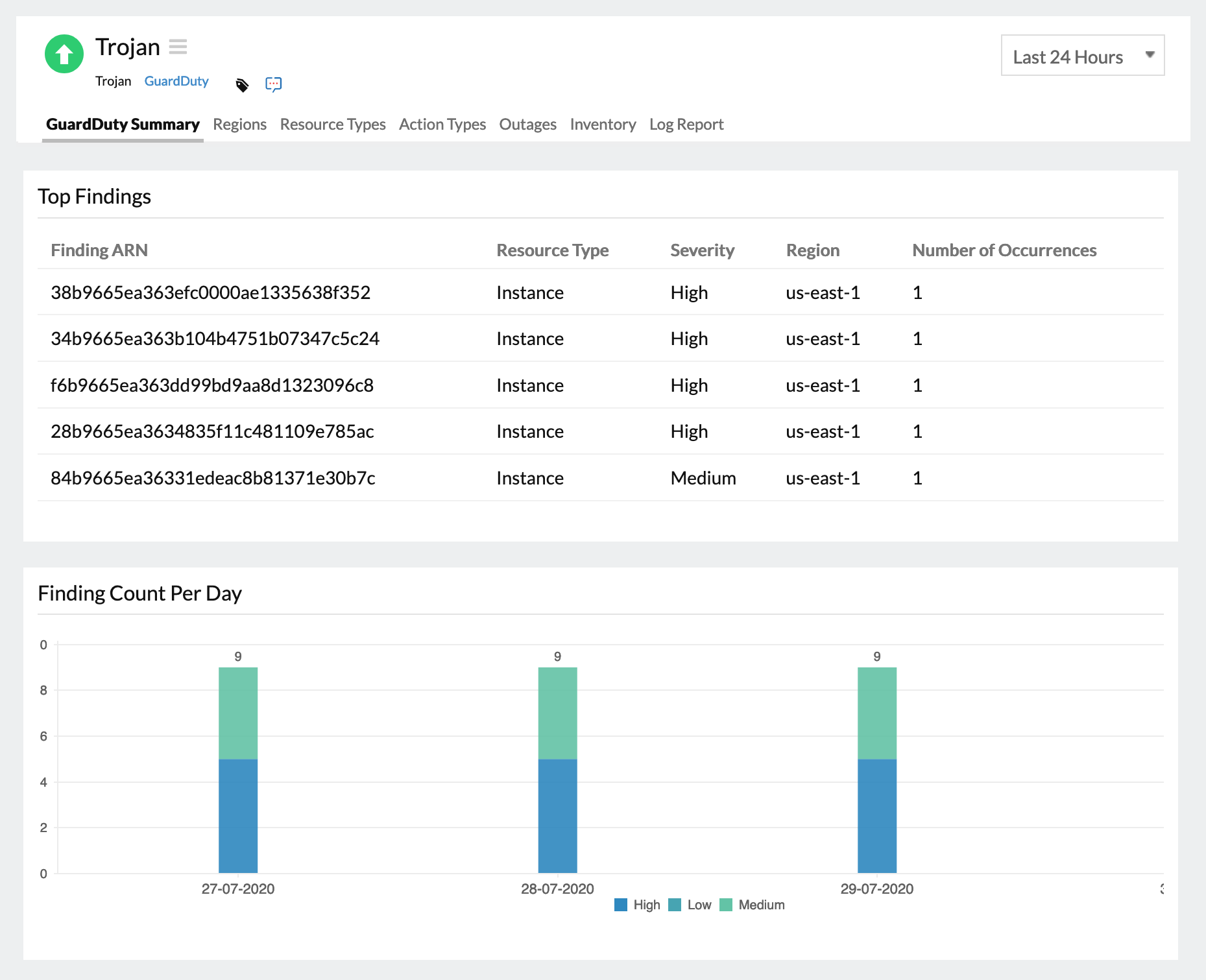
GuardDuty Finding Summary
Receive alerts on all AWS account requests that use root credentials. Obtain insights about similar major issues in your cloud infrastructure grouped according to its resource type, severity, or region. Choose to receive persistent notifications on each error until the alarm is acknowledged.
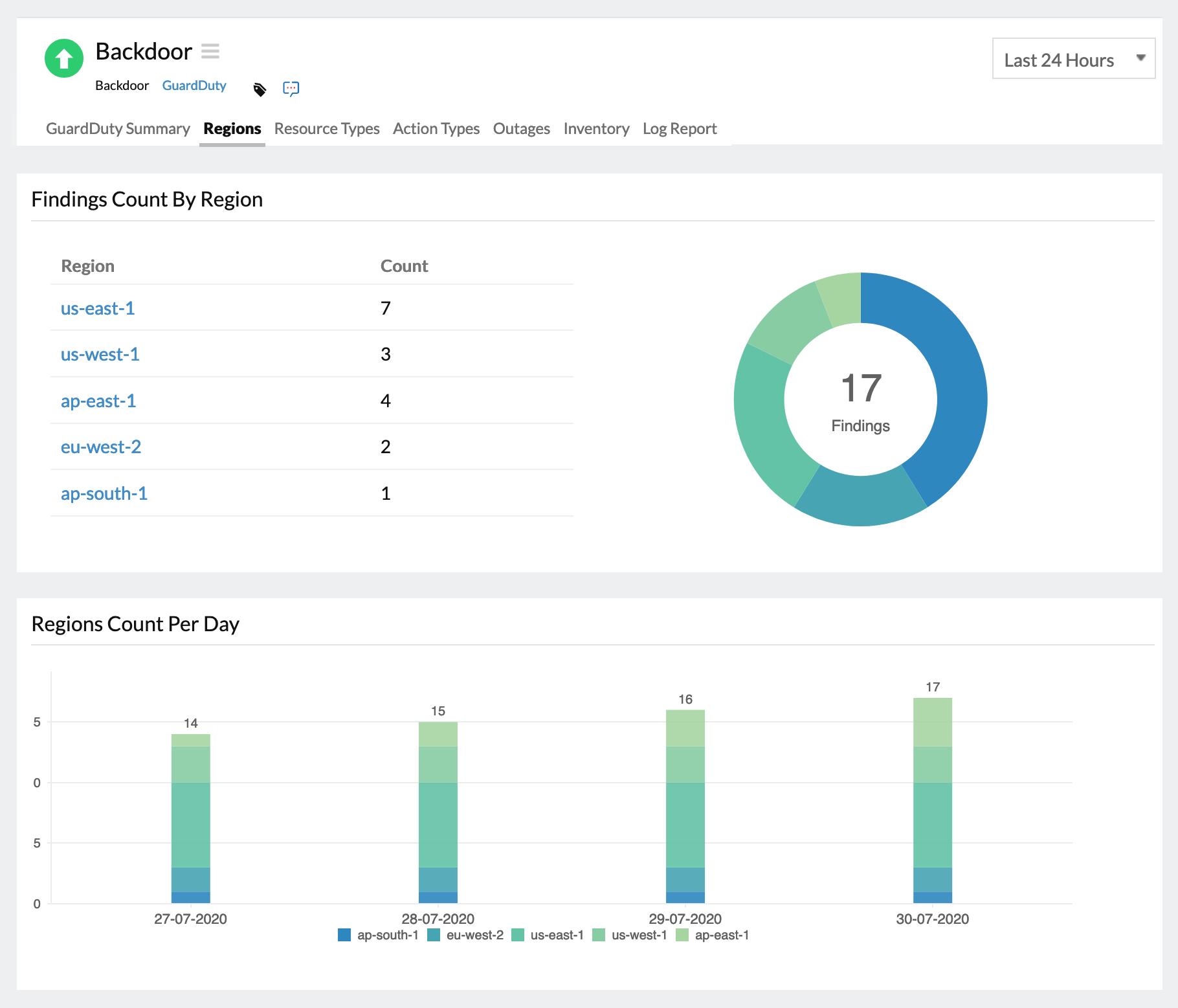
Reporting Region-wise
Identify the key regions where an Amazon Elastic Cloud Compute(EC2) may have been compromised due to denial-of-service (DoS) attacks with public routable IP addresses. Understand the demographic details of a particular threat by using the charts visualized according to findings count, and regions affected in a day.
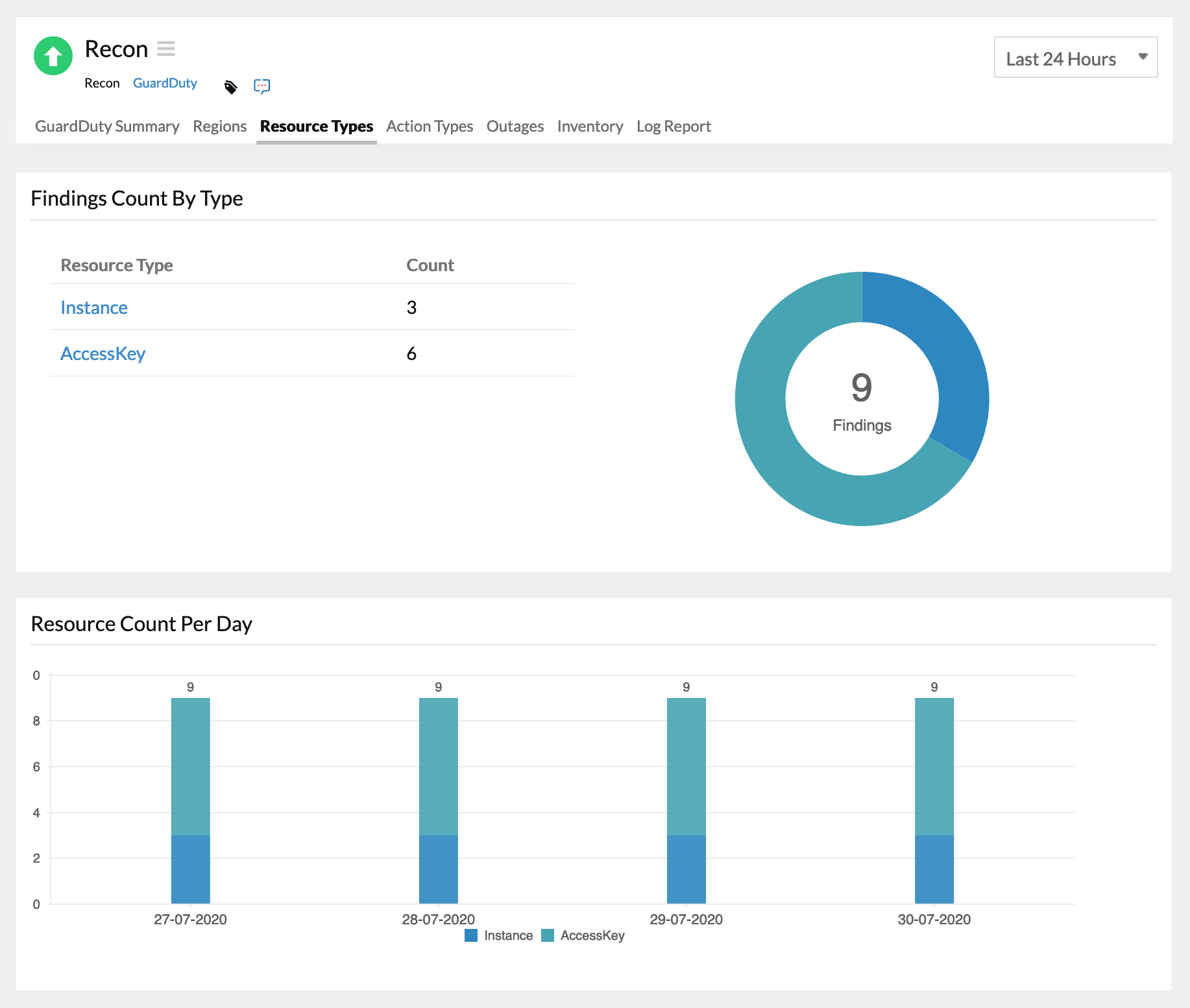
Affected Resources
Identify the resources and the number of times they are affected by cryptocurrency mining-related, or unauthorized access-related activities. Receive insights about the exact instances that are vulnerable, and take precautionary measures to safeguard the instance for different GuardDuty findings.
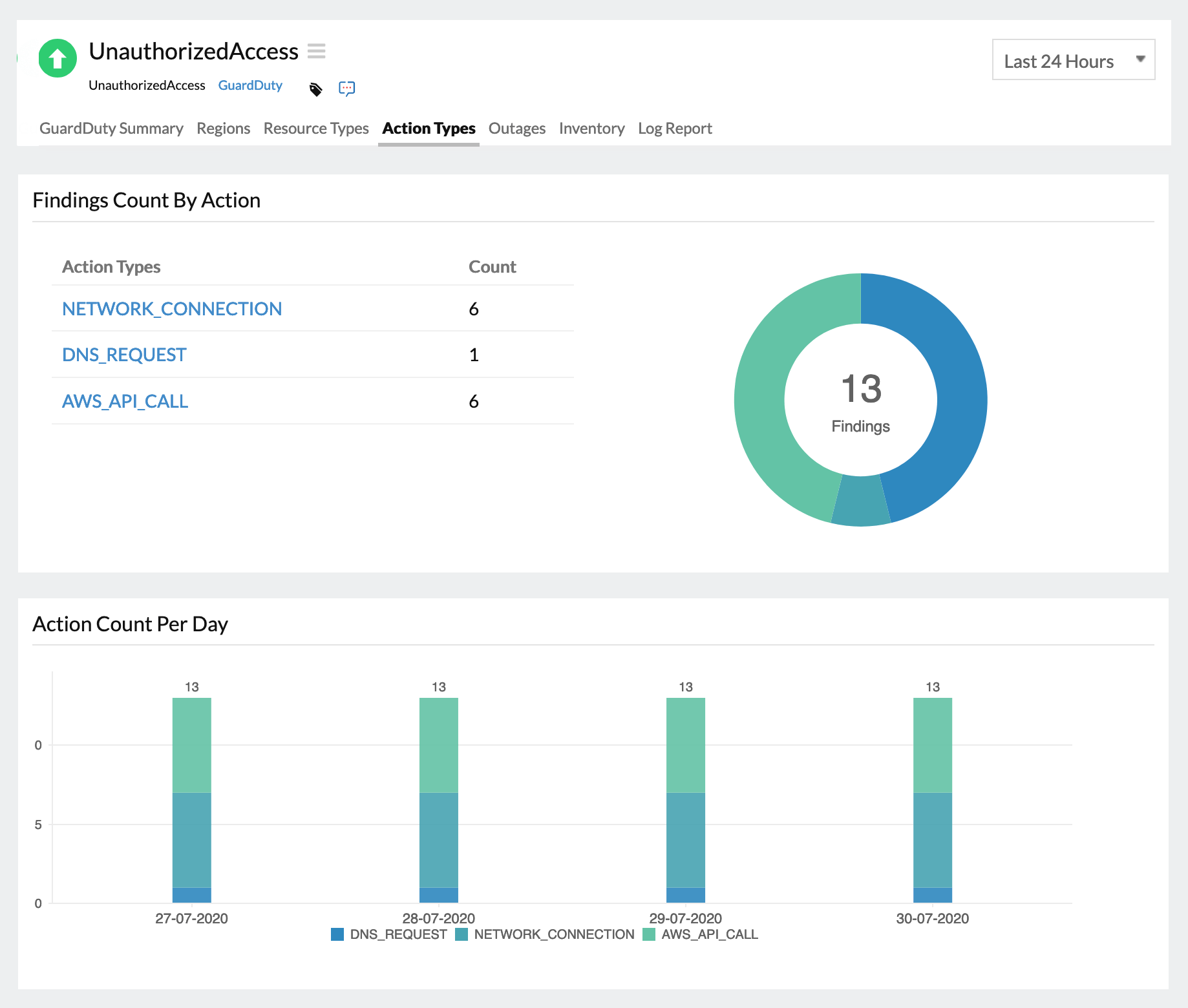
Triggered Actions
Observe and get alerted if the Amazon EC2 instances have been compromised by any malicious activity using the Tor Network, an open-source privacy network that permits users to browse the web anonymously. Set thresholds and get alerted when there is a threshold breach on various action types, like instance API calls, DNS requests, or network connections.